#加密市场行情震荡rsETH ATTACK UPDATE HOW A SINGLE FORGED MESSAGE SHATTERED $10 BILLION IN DEFI
THE ATTACK THAT CHANGED DEFI FOREVER
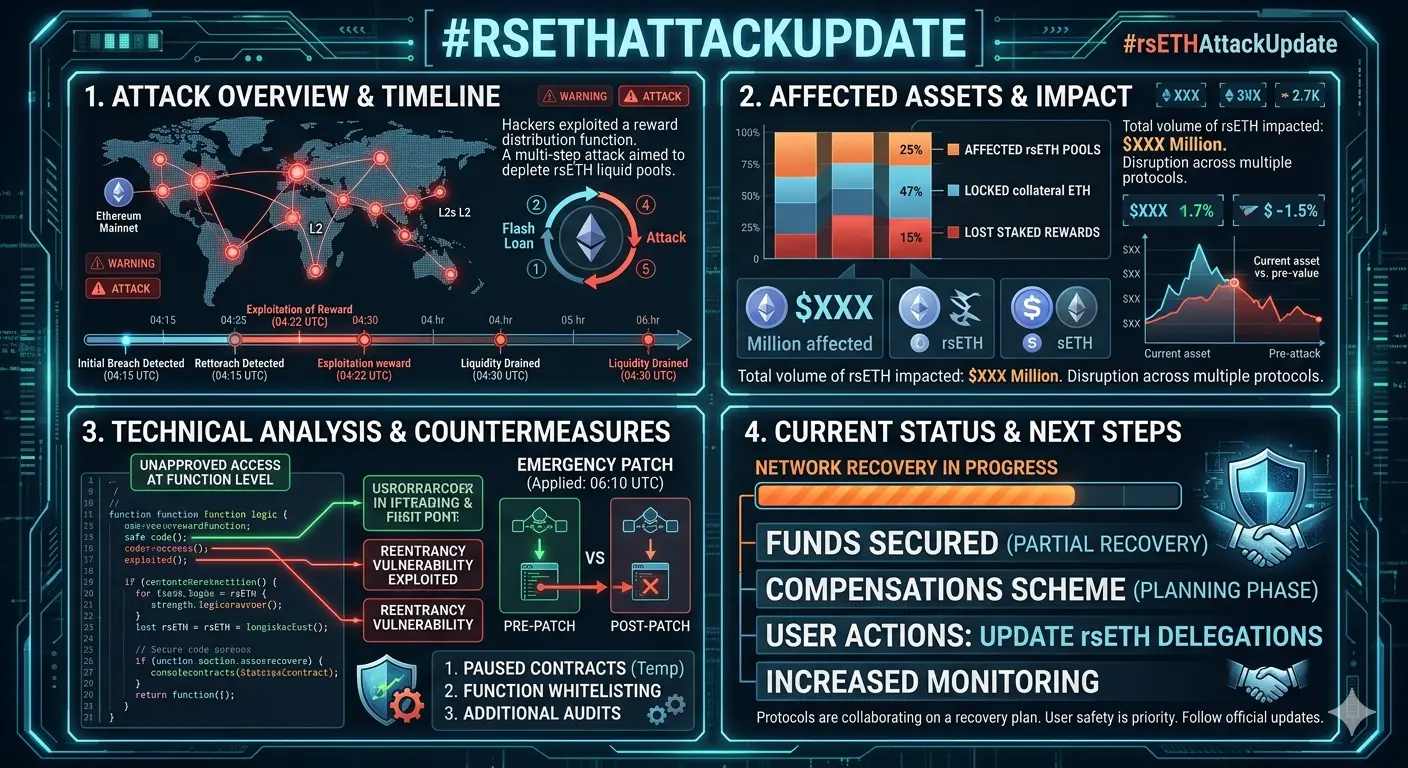
At exactly 17:35 UTC on April 18, 2026, a single forged cross-chain message triggered the largest DeFi exploit of the year. KelpDAO's LayerZero-powered rsETH bridge was drained of 116,500 rsETH approximately $292 million in a matter of minutes. No smart contract was broken. No Solidity code was exploited. The entire attack happened in the invisible layer between blockchains, in the off-chain verification infrastructure that DeFi has quietly depended on without fully understanding its vulnerability. By the time the dust settled 24 hours later, total DeFi value locked had collapsed from $99.5 billion to $85.21 billion a $14 billion destruction of value from a single exploit. This is the rsETH attack update that every DeFi participant needs to understand completely.
WHAT IS KELPDAO AND WHY DID IT MATTER
KelpDAO is a liquid restaking protocol built on Ethereum and EigenLayer. Users deposit ETH, the protocol routes it through EigenLayer's restaking infrastructure to earn additional yield on top of standard staking rewards, and issues rsETH a tradeable receipt token representing the restaked position plus accrued rewards. By April 2026, rsETH had crossed $1 billion in total value locked and was integrated as collateral across most of the major lending markets and yield platforms in DeFi. rsETH was live across more than 20 blockchain networks including Arbitrum, Base, Linea, Mantle, Blast, and Scroll, using LayerZero's OFT standard to move between chains. The bridge that was drained held the reserves backing every single one of those wrapped rsETH tokens across every Layer 2 deployment. When that bridge was emptied, 18% of the entire rsETH circulating supply became unbacked simultaneously across 20+ chains.
HOW THE ATTACK WAS EXECUTED THE TECHNICAL BREAKDOWN
The attack was not a smart contract hack. Every on-chain transaction looked completely valid. Signatures were verified. Messages were properly formatted. The exploit was against the off-chain infrastructure layer — specifically LayerZero's Decentralized Verifier Network, the system that confirms whether cross-chain messages are legitimate before the destination chain acts on them.
KelpDAO's rsETH bridge used a 1-of-1 DVN configuration. This meant only one entity the LayerZero Labs DVN was required to verify and approve cross-chain messages. No second verifier, no independent confirmation, no redundancy. One verifier. One point of failure.
The Lazarus Group North Korea's state-sponsored hacking unit identified this seam and executed a three-part infrastructure attack. First, they compromised two internal RPC nodes that fed market data to the LayerZero verifier, poisoning the data feed with false information. Second, they launched a DDoS attack against the clean backup nodes, forcing the system to failover to the already-compromised infrastructure. Third, with the verifier now running entirely on poisoned nodes, they injected a forged LayerZero cross-chain message nonce 308 that told the Ethereum bridge contract a valid burn had occurred on the source chain, triggering the release of 116,500 rsETH to an attacker-controlled wallet. The entire operation used pre-funded wallets sourced through Tornado Cash approximately 10 hours before the attack, confirming this was a long-planned, state-level operation and not an opportunistic exploit.
Within minutes, the attacker deposited the stolen rsETH as collateral on Aave and borrowed over $236 million in WETH against it using unbacked tokens as collateral for a real loan. The $292 million theft had turned into a $236 million WETH extraction before most users knew anything had happened.
THE 46-MINUTE RESPONSE THAT SAVED $100 MILLION
KelpDAO's emergency response team identified the attack and activated the emergency pauser multisig at 18:21 UTC exactly 46 minutes after the initial drain. The protocol-wide pause froze deposits, withdrawals, and the rsETH token itself across mainnet and all L2 deployments. At 18:26 UTC and 18:28 UTC, two follow-up drain attempts by the attacker each targeting an additional 40,000 rsETH worth approximately $100 million both reverted against the frozen contracts. The 46-minute response window is the difference between a $292 million exploit and a $492 million catastrophe. The quick action of KelpDAO's emergency team is the only reason the damage was not almost double.
THE CONTAGION THAT SWEPT THROUGH DEFI
The downstream damage moved faster than any emergency pause could contain. Aave the largest lending protocol in DeFi with over $20 billion in total value locked froze rsETH markets on both V3 and V4 within hours. ETH utilization on Aave briefly spiked to 100% as users scrambled to withdraw. The AAVE token dropped approximately 10-20% as traders priced in potential bad debt exposure. SparkLend and Fluid both froze their rsETH markets. Lido Finance paused deposits into its earnETH product due to rsETH exposure. Ethena temporarily paused its LayerZero OFT bridges from Ethereum mainnet as a precautionary measure. The total DeFi TVL collapsed from $99.5 billion to $85.21 billion in a single day $14 billion erased from across the ecosystem by one exploit on one bridge.
Aave's own incident analysis found that the exploit created unbacked collateral used to borrow roughly $190 million, leaving the protocol facing potential bad debt between $123 million and $230 million depending on how KelpDAO allocates the shortfall across rsETH holders.
THE LAZARUS GROUP ATTRIBUTION
This was not a random hack. LayerZero formally attributed the attack to North Korea's Lazarus Group the same state-sponsored hacking unit linked to the $285 million Drift exploit on April 1, 2026, and dozens of prior crypto thefts totaling billions of dollars across multiple years. The Lazarus Group is the most prolific and technically sophisticated crypto hacking operation in the world, and their involvement in two of the three largest DeFi exploits of 2026 within 18 days confirms a systematic, coordinated campaign targeting DeFi infrastructure at the infrastructure layer rather than the contract layer.
ARBITRUM'S EMERGENCY FREEZE UNPRECEDENTED INTERVENTION
On April 21, 2026 three days after the exploit the Arbitrum Security Council executed the most significant emergency intervention in Layer 2 history. The 12-member council, operating under a 9-of-12 multisig, seized 30,766 ETH from the attacker's address on Arbitrum One and transferred it to a frozen intermediary wallet. The transfer completed at 11:26 p.m. ET on April 21. Those funds cannot move again without a formal Arbitrum governance vote. The intervention recovered approximately $71.15 million roughly 29% of the ETH the attacker had accumulated on Arbitrum. The remaining 75,701 ETH worth approximately $175 million on Ethereum mainnet had already been moved and was being laundered through Thorchain and other privacy tools before the freeze could be extended.
The freeze sparked immediate debate about decentralization. If a 12-person council can freeze assets on Arbitrum, what does that mean for the permissionless ownership guarantee that Layer 2 promises? Supporters called it DeFi defending itself against state-sponsored crime. Critics called it proof that Arbitrum is ultimately a multisig wallet with the power to override user asset control.
THE LAYERZERO VS KELPDAO BLAME WAR
The post-exploit period produced a full public dispute between LayerZero and KelpDAO over who bears responsibility. LayerZero published a post-mortem stating that KelpDAO chose a 1-of-1 DVN configuration despite explicit recommendations to adopt multi-verifier redundancy, and announced it would immediately stop signing messages for any application running a single-verifier setup forcing a broad migration across all LayerZero integrations.
KelpDAO fired back, claiming the 1-of-1 configuration was the default setup shipped by LayerZero for new deployments, that LayerZero's own documentation and public deployment code promotes single-source verification, and that the compromised infrastructure the RPC nodes and DVN servers was built and operated entirely by LayerZero, not Kelp. Security researchers sided partially with Kelp, with prominent developer banteg publishing a technical review confirming that LayerZero's reference deployment code ships with single-source verification as the default across major chains.
The result is a damage-splitting standoff with no clear resolution. Both parties have promised full root-cause post-mortems. The deeper question whether every other 1-of-1 OFT application currently running on LayerZero is exposed to the same class of attack remains unanswered.
WHAT THIS MEANS FOR DEFI GOING FORWARD
The KelpDAO exploit is not just another hack. It is a category-defining event that exposed a structural blind spot across the entire cross-chain DeFi ecosystem. The attack sits in the same historical family as Ronin and Nomad bridge failures where central verification checkpoints became the high-value target. But it goes further, because the on-chain contracts were never touched. Every transaction on-chain was valid. The failure was in the invisible off-chain infrastructure that DeFi has treated as a solved problem for years.
The lessons are clear and immediate. Multi-verifier DVN configurations are now non-negotiable for any bridge holding significant value. Configuration audits reviewing deployment settings, not just smart contract code must become standard practice. Cross-chain invariant monitoring that continuously verifies tokens released on destination chains match tokens burned on source chains is the new minimum bar for bridge security. And the question of how DeFi handles state-sponsored hacking operations with the resources and patience of a national government has no clean answer yet.
The $292 million theft. The $14 billion TVL destruction. The $230 million in potential Aave bad debt. The 30,766 ETH frozen by Arbitrum. The Lazarus Group attribution. All of it points to one conclusion DeFi's cross-chain infrastructure layer is the most underprotected surface in the entire ecosystem, and the most sophisticated hackers in the world have identified that fact and are systematically exploiting it.
The rsETH attack is not a warning. It is a verdict. Fix the infrastructure layer, or lose everything that sits on top of it.
#rsETHAttackUpdate
THE ATTACK THAT CHANGED DEFI FOREVER
At exactly 17:35 UTC on April 18, 2026, a single forged cross-chain message triggered the largest DeFi exploit of the year. KelpDAO's LayerZero-powered rsETH bridge was drained of 116,500 rsETH approximately $292 million in a matter of minutes. No smart contract was broken. No Solidity code was exploited. The entire attack happened in the invisible layer between blockchains, in the off-chain verification infrastructure that DeFi has quietly depended on without fully understanding its vulnerability. By the time the dust settled 24 hours later, total DeFi value locked had collapsed from $99.5 billion to $85.21 billion a $14 billion destruction of value from a single exploit. This is the rsETH attack update that every DeFi participant needs to understand completely.
WHAT IS KELPDAO AND WHY DID IT MATTER
KelpDAO is a liquid restaking protocol built on Ethereum and EigenLayer. Users deposit ETH, the protocol routes it through EigenLayer's restaking infrastructure to earn additional yield on top of standard staking rewards, and issues rsETH a tradeable receipt token representing the restaked position plus accrued rewards. By April 2026, rsETH had crossed $1 billion in total value locked and was integrated as collateral across most of the major lending markets and yield platforms in DeFi. rsETH was live across more than 20 blockchain networks including Arbitrum, Base, Linea, Mantle, Blast, and Scroll, using LayerZero's OFT standard to move between chains. The bridge that was drained held the reserves backing every single one of those wrapped rsETH tokens across every Layer 2 deployment. When that bridge was emptied, 18% of the entire rsETH circulating supply became unbacked simultaneously across 20+ chains.
HOW THE ATTACK WAS EXECUTED THE TECHNICAL BREAKDOWN
The attack was not a smart contract hack. Every on-chain transaction looked completely valid. Signatures were verified. Messages were properly formatted. The exploit was against the off-chain infrastructure layer — specifically LayerZero's Decentralized Verifier Network, the system that confirms whether cross-chain messages are legitimate before the destination chain acts on them.
KelpDAO's rsETH bridge used a 1-of-1 DVN configuration. This meant only one entity the LayerZero Labs DVN was required to verify and approve cross-chain messages. No second verifier, no independent confirmation, no redundancy. One verifier. One point of failure.
The Lazarus Group North Korea's state-sponsored hacking unit identified this seam and executed a three-part infrastructure attack. First, they compromised two internal RPC nodes that fed market data to the LayerZero verifier, poisoning the data feed with false information. Second, they launched a DDoS attack against the clean backup nodes, forcing the system to failover to the already-compromised infrastructure. Third, with the verifier now running entirely on poisoned nodes, they injected a forged LayerZero cross-chain message nonce 308 that told the Ethereum bridge contract a valid burn had occurred on the source chain, triggering the release of 116,500 rsETH to an attacker-controlled wallet. The entire operation used pre-funded wallets sourced through Tornado Cash approximately 10 hours before the attack, confirming this was a long-planned, state-level operation and not an opportunistic exploit.
Within minutes, the attacker deposited the stolen rsETH as collateral on Aave and borrowed over $236 million in WETH against it using unbacked tokens as collateral for a real loan. The $292 million theft had turned into a $236 million WETH extraction before most users knew anything had happened.
THE 46-MINUTE RESPONSE THAT SAVED $100 MILLION
KelpDAO's emergency response team identified the attack and activated the emergency pauser multisig at 18:21 UTC exactly 46 minutes after the initial drain. The protocol-wide pause froze deposits, withdrawals, and the rsETH token itself across mainnet and all L2 deployments. At 18:26 UTC and 18:28 UTC, two follow-up drain attempts by the attacker each targeting an additional 40,000 rsETH worth approximately $100 million both reverted against the frozen contracts. The 46-minute response window is the difference between a $292 million exploit and a $492 million catastrophe. The quick action of KelpDAO's emergency team is the only reason the damage was not almost double.
THE CONTAGION THAT SWEPT THROUGH DEFI
The downstream damage moved faster than any emergency pause could contain. Aave the largest lending protocol in DeFi with over $20 billion in total value locked froze rsETH markets on both V3 and V4 within hours. ETH utilization on Aave briefly spiked to 100% as users scrambled to withdraw. The AAVE token dropped approximately 10-20% as traders priced in potential bad debt exposure. SparkLend and Fluid both froze their rsETH markets. Lido Finance paused deposits into its earnETH product due to rsETH exposure. Ethena temporarily paused its LayerZero OFT bridges from Ethereum mainnet as a precautionary measure. The total DeFi TVL collapsed from $99.5 billion to $85.21 billion in a single day $14 billion erased from across the ecosystem by one exploit on one bridge.
Aave's own incident analysis found that the exploit created unbacked collateral used to borrow roughly $190 million, leaving the protocol facing potential bad debt between $123 million and $230 million depending on how KelpDAO allocates the shortfall across rsETH holders.
THE LAZARUS GROUP ATTRIBUTION
This was not a random hack. LayerZero formally attributed the attack to North Korea's Lazarus Group the same state-sponsored hacking unit linked to the $285 million Drift exploit on April 1, 2026, and dozens of prior crypto thefts totaling billions of dollars across multiple years. The Lazarus Group is the most prolific and technically sophisticated crypto hacking operation in the world, and their involvement in two of the three largest DeFi exploits of 2026 within 18 days confirms a systematic, coordinated campaign targeting DeFi infrastructure at the infrastructure layer rather than the contract layer.
ARBITRUM'S EMERGENCY FREEZE UNPRECEDENTED INTERVENTION
On April 21, 2026 three days after the exploit the Arbitrum Security Council executed the most significant emergency intervention in Layer 2 history. The 12-member council, operating under a 9-of-12 multisig, seized 30,766 ETH from the attacker's address on Arbitrum One and transferred it to a frozen intermediary wallet. The transfer completed at 11:26 p.m. ET on April 21. Those funds cannot move again without a formal Arbitrum governance vote. The intervention recovered approximately $71.15 million roughly 29% of the ETH the attacker had accumulated on Arbitrum. The remaining 75,701 ETH worth approximately $175 million on Ethereum mainnet had already been moved and was being laundered through Thorchain and other privacy tools before the freeze could be extended.
The freeze sparked immediate debate about decentralization. If a 12-person council can freeze assets on Arbitrum, what does that mean for the permissionless ownership guarantee that Layer 2 promises? Supporters called it DeFi defending itself against state-sponsored crime. Critics called it proof that Arbitrum is ultimately a multisig wallet with the power to override user asset control.
THE LAYERZERO VS KELPDAO BLAME WAR
The post-exploit period produced a full public dispute between LayerZero and KelpDAO over who bears responsibility. LayerZero published a post-mortem stating that KelpDAO chose a 1-of-1 DVN configuration despite explicit recommendations to adopt multi-verifier redundancy, and announced it would immediately stop signing messages for any application running a single-verifier setup forcing a broad migration across all LayerZero integrations.
KelpDAO fired back, claiming the 1-of-1 configuration was the default setup shipped by LayerZero for new deployments, that LayerZero's own documentation and public deployment code promotes single-source verification, and that the compromised infrastructure the RPC nodes and DVN servers was built and operated entirely by LayerZero, not Kelp. Security researchers sided partially with Kelp, with prominent developer banteg publishing a technical review confirming that LayerZero's reference deployment code ships with single-source verification as the default across major chains.
The result is a damage-splitting standoff with no clear resolution. Both parties have promised full root-cause post-mortems. The deeper question whether every other 1-of-1 OFT application currently running on LayerZero is exposed to the same class of attack remains unanswered.
WHAT THIS MEANS FOR DEFI GOING FORWARD
The KelpDAO exploit is not just another hack. It is a category-defining event that exposed a structural blind spot across the entire cross-chain DeFi ecosystem. The attack sits in the same historical family as Ronin and Nomad bridge failures where central verification checkpoints became the high-value target. But it goes further, because the on-chain contracts were never touched. Every transaction on-chain was valid. The failure was in the invisible off-chain infrastructure that DeFi has treated as a solved problem for years.
The lessons are clear and immediate. Multi-verifier DVN configurations are now non-negotiable for any bridge holding significant value. Configuration audits reviewing deployment settings, not just smart contract code must become standard practice. Cross-chain invariant monitoring that continuously verifies tokens released on destination chains match tokens burned on source chains is the new minimum bar for bridge security. And the question of how DeFi handles state-sponsored hacking operations with the resources and patience of a national government has no clean answer yet.
The $292 million theft. The $14 billion TVL destruction. The $230 million in potential Aave bad debt. The 30,766 ETH frozen by Arbitrum. The Lazarus Group attribution. All of it points to one conclusion DeFi's cross-chain infrastructure layer is the most underprotected surface in the entire ecosystem, and the most sophisticated hackers in the world have identified that fact and are systematically exploiting it.
The rsETH attack is not a warning. It is a verdict. Fix the infrastructure layer, or lose everything that sits on top of it.
#rsETHAttackUpdate