SlowMist Reveals the Drift Attack Chain: Multi-Signature Mechanism Change, Administrator Privileges Leaked

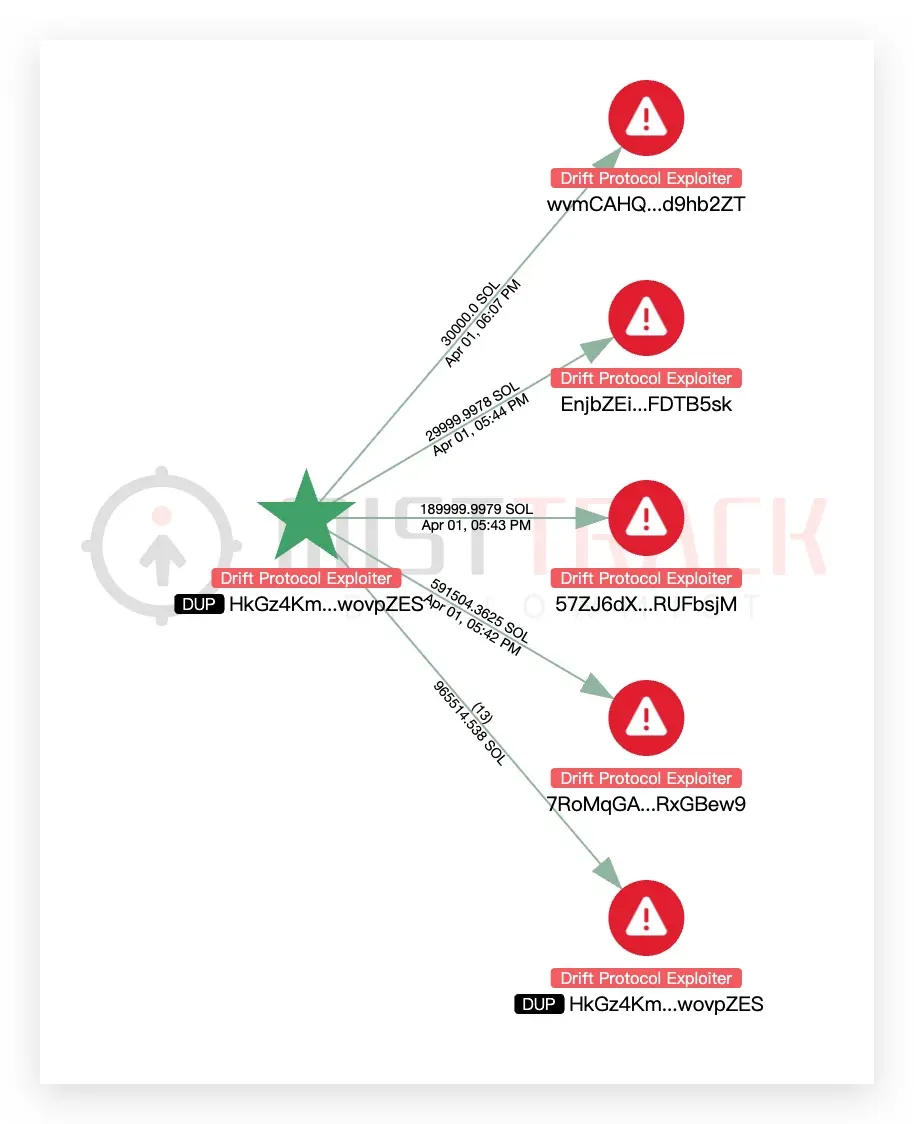
SlowMist, an on-chain security firm (SlowMist), released a technical analysis on April 2, revealing the key prerequisites for the Drift Protocol hack incident: about a week before the attack, Drift made adjustments to the multi-signature mechanism, and it did not synchronously set up a time-lock protection mechanism. The attacker then obtained administrator privileges, forged CVT tokens, manipulated the oracle, and shut down the security module, systematically extracting high-value assets from the fund pool.
SlowMist reconstructs the attack’s warning signs: changing multisig without a time lock is the core vulnerability
 (Source: SlowMist)
(Source: SlowMist)
SlowMist’s analysis reveals the most alarming pre-attack trigger in this incident: about a week before the tokens were stolen, Drift changed the multisig mechanism to a “2/5” mode without setting any time lock, while also introducing four new signers.
A time lock is a necessary security complement for multisig mechanisms in protocol security design. It establishes a mandatory waiting period (typically 24–48 hours or longer) before executing high-risk configuration changes, giving the community and security organizations enough time to detect anomalies and intervene. Without a time lock, once a new signer’s private key is stolen or maliciously controlled, the attacker can immediately carry out administrator-level operations with no waiting buffer.
The multisig architecture change that occurred one week before the tokens were stolen (introducing four new signers) is highly suspicious in terms of timing, and is the warning point receiving the most attention in this security analysis.
Reconstructing the attack steps: from administrator leak to 105,969 ETH stolen
According to SlowMist’s technical analysis, after obtaining administrator control, the attacker systematically emptied assets by executing the following steps:
Forging CVT tokens: forging fake tokens within the protocol, bypassing the normal asset validation logic
Manipulating the Oracle: changing the protocol’s external price source so that on-chain pricing is distorted, creating favorable conditions for subsequent extraction
Shutting down security mechanisms: disabling the protocol’s built-in risk control and security constraint modules, removing obstacles to asset extraction
Transferring high-value assets: systematically extracting highly liquid assets from the fund pool to complete the final asset emptying
At present, the stolen funds have mainly been consolidated to Ethereum addresses, totaling about 105,969 ETH (about $226 million). SlowMist states that the related fund flows are still being tracked.
ZachXBT calls out Circle: industry strongly criticizes USDC that wasn’t frozen for hours
On the same day, on-chain sleuth ZachXBT issued strong criticism of Circle. He pointed out that during the U.S. trading hours while Drift was being hacked, USDC in the tens of millions of dollars was bridged from Solana to Ethereum via a cross-chain protocol. The entire process was “ongoing for several hours with no intervention,” and after the related funds had completed the full transfer, Circle “again took no action.”
ZachXBT also revealed another issue Circle had previously faced: Circle mistakenly froze more than 16 business hot wallets, and the related unfreezing process is still ongoing to this day. He specifically named Circle CEO Jeremy Allaire, saying that Circle’s performance has had a negative impact on the entire crypto industry.
These allegations have sparked widespread discussion in the industry about what proactive intervention responsibilities stablecoin issuers should bear in security incidents.
Frequently Asked Questions
Why is not setting a time lock when modifying the multisig the core issue in this attack?
A time lock is a key security safeguard for multisig mechanisms. It sets a mandatory waiting period before executing high-privilege operations, giving the community and security organizations time to detect anomalies and take action. When Drift adjusted the multisig architecture, it did not set a time lock, meaning that once the credentials of the newly added signer were leaked, the attacker could immediately execute administrator actions, bypassing the community’s final line of oversight. The timing of the change introducing four new signers one week before the theft is the most closely scrutinized point in the current investigation.
What responsibility should Circle bear in this incident?
ZachXBT’s criticism points to Circle’s lack of real-time monitoring and intervention during the large-scale cross-chain USDC transfers. As the issuer of USDC, Circle has the technical ability to freeze involved addresses, but it did not take action during the hours-long transfer process. This controversy touches on the boundary of proactive intervention responsibilities of stablecoin issuers in DeFi security incidents, and is a core topic hotly discussed in the industry right now.
What is the technical significance of the combination of forging CVT tokens and manipulating the oracle?
Forging CVT tokens allows an attacker to manufacture fake liquidity or collateral within a protocol. Manipulating the oracle causes the protocol to use distorted market data when pricing. Combined, this makes the protocol “believe” it has sufficient collateral support, thereby allowing the attacker to extract assets far exceeding what they are actually entitled to—an established classic tactic in smart contract attacks, and one that has appeared in multiple DeFi hack cases.
Related Articles
Chainalysis Details 'Shadow Crypto Economy' Exposure as Grinex Suspends Operations
Rhea Finance Suffers a $18.4 Million Loss After an Oracle Attack: ZachXBT Warns, Tether Freezes 4.34 Million USDT, and the Attacker Returns Some Funds
eth.limo DNS Under Attack, Vitalik Urges Users to Pause Access and Switch to IPFS
Sanctioned Exchange Grinex Hit by $13.7M Hack; Blames Foreign Intelligence Services
Figure Faces Short Seller Accusations Over Blockchain Integration Claims; FIGR Stock Down 53% From January Peak
Houston Crypto Fraudster Sentenced to 23 Years for $20M Meta-1 Coin Scam